
Article written by Axis Geffen
When I started in the investigations industry, faking a photograph was easy…if you had infinite access to money and technology! However, for the majority of people, it wasn’t very easy to do at all. Even if you did manage to successfully tamper with an image, you still had to deal with or destroy the negative(s). In the modern age, altering or deepfaking an image isn’t as challenging. If you’re not familiar with the term, a deepfake is where a person in an existing image or video is replaced with someone else’s face. Sometimes it is done as a joke, while other times it is done to try an incriminate someone.
So, how can you tell if the image is real or fake? And is there any image that you can never tell the difference? What if someone tries a deepfake tactic to damage their ex’s case during a separation or divorce?
The truth is that for a long time, those were questions that haunted even professional investigators. Further to this, the context of a photo plays a big role in forming the answer, so, it was, and can still be difficult to tell. However, special utilities have been developed for use in forensics and as such, there are ways to verify if a photo has been altered.
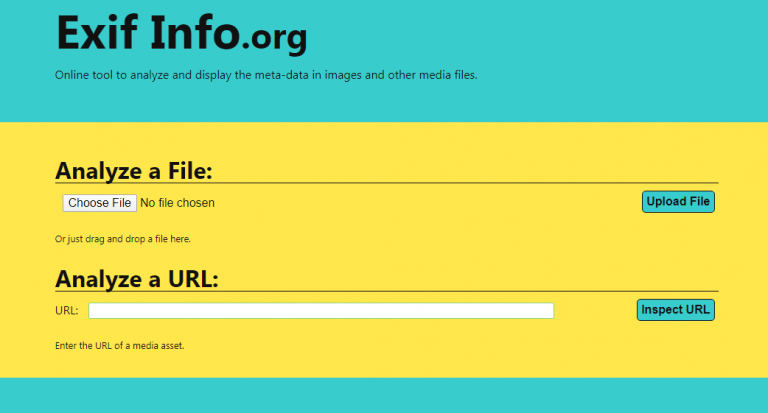
EXIF Information: This has been a go-to for many investigators and analysts for quite a while. Whenever you take a photo with any digital device, that device writes a bunch of “hidden code” in the background of the file. You can’t see it, but it’s there. The code will reveal information including what lens is attached to the model of iPhone that was used to take the photo, to the geographic coordinates of exactly where that photo was taken. It’s really pretty cool, but on its own, that information is not usually enough because it can be removed from the photo after it is uploaded to the computer.
Digital Hash Code: Hashing is the practice of using an algorithm to map data of any size to a fixed length. When trying to detect a deepfake, the image is cryptographically analyzed and a set “hash” value is given to that image in a specific number of characters. The more the characters, the more specific the value; however, the neat thing about this is that the code is unbreakable. No matter what computer you use, that code will always be the same unless something (absolutely anything) in the photo has changed. The catch 22 on this is that if you don’t have the original photo – then you don’t have anything to compare it to. So, while you’ll know if the image was tampered with after you took it into evidence, you won’t be able to tell if the image was changed before you ever saw it from this method alone.
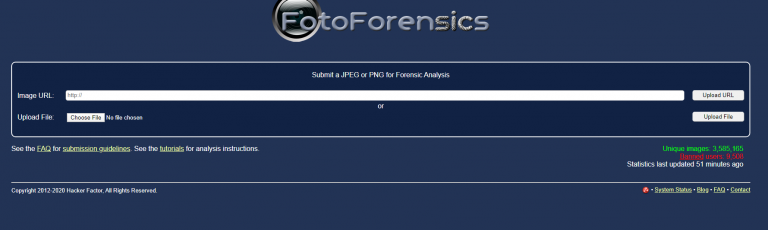
FotoForensics: This is also an option to consider as this site contains various tools to electronically break down and analyze the photos. However, there is no digital one-stop-shop for getting a conclusive answer.
Naked Eye Enhanced:At the end of the day, it usually comes down to what a human being has personally observed and documented in each image. All of the other tools are great, but nothing beats the trained and experienced naked eye with properly calibrated magnification tools. There are telltale signs in any deepfake photo that trained professionals look out for.
When trying to verify evidence of this nature, having access to the true original and the device that took the picture will prove to be most helpful. However that isn’t always possible. If that is the case, multiple tests may have to be conducted and an expert may be required.
%201.png?)
